Data security for the new age
Research Issues
Lattice‐based Cryptography, Homomorphic Encryption, Post‐quantum Security, Security Proofs, Side‐channel Attacks, Dynamic Message Authentication, Confidential Querying, Network Security, Massively Parallel Computation, Blockchain
Research Areas
Cryptography, Homomorphic Encryption, Penetration Testing, ATM Security, Blockchain Applications, Secure Web Applications
Majors Preparation and Interests
Mathematics – Algebraic Number Theory, Lattice Invariants, Diophantine System Solving, Probabilistic Analysis, Modular Interval Arithmetic CSI – Complexity Analysis, Proofs of Security, Penetration Testing CmpE, CS – Optimizations, High Performance Implementations, Parallel Algorithms, Logic circuit obfuscation, FPGAs, GPUs MIS – Bringing these solutions to market, distributed record management, confidentiality preservation, secure data‐mining
Key Elements
Computational Mathematics, Management Information Systems, Healthcare IT, High‐Performance Computing, Cryptography, Quantum Computing, ATM Security, Biometrics, Pen Testing, Cryptographic Currencies
Goals
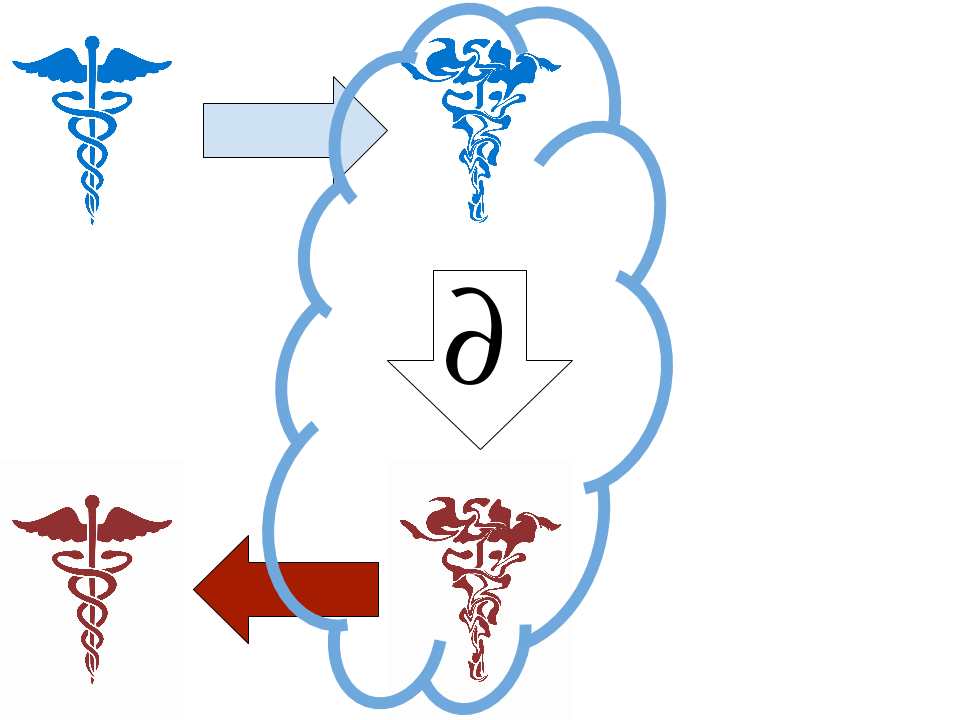
The Cloud Crypto team has several aims. We are working actively on ATM security using biometrics, Blockchain voting systems, Penetration Testing, Secure Software Design, and Fully Homomorphic Encryption. Overall, this project aims to create practical and economically disruptive security solutions. Currently, every medical, financial, and governmental institution that must update and search confidential records has to have secure hardware, secure software, and secure staff. They are unable to take full advantage of the internet‐sized economies of scale that drive our modern economy. The central technological hurdle is creating practical security schemes that allow untrusted machines to perform queries and updates on encrypted data. Until very recently this was considered impossible, but in the last few years theoretical, yet infeasible, schemes have been devised. This project aims to push the boundaries of cryptographic applications. From blockchain, to an untrusted cloud, into our post-quantum future. We will need both technological and political breakthroughs to progress.
Faculty
Andy Novocin, PH.D., Professor, ECE, andynovo@udel.edu